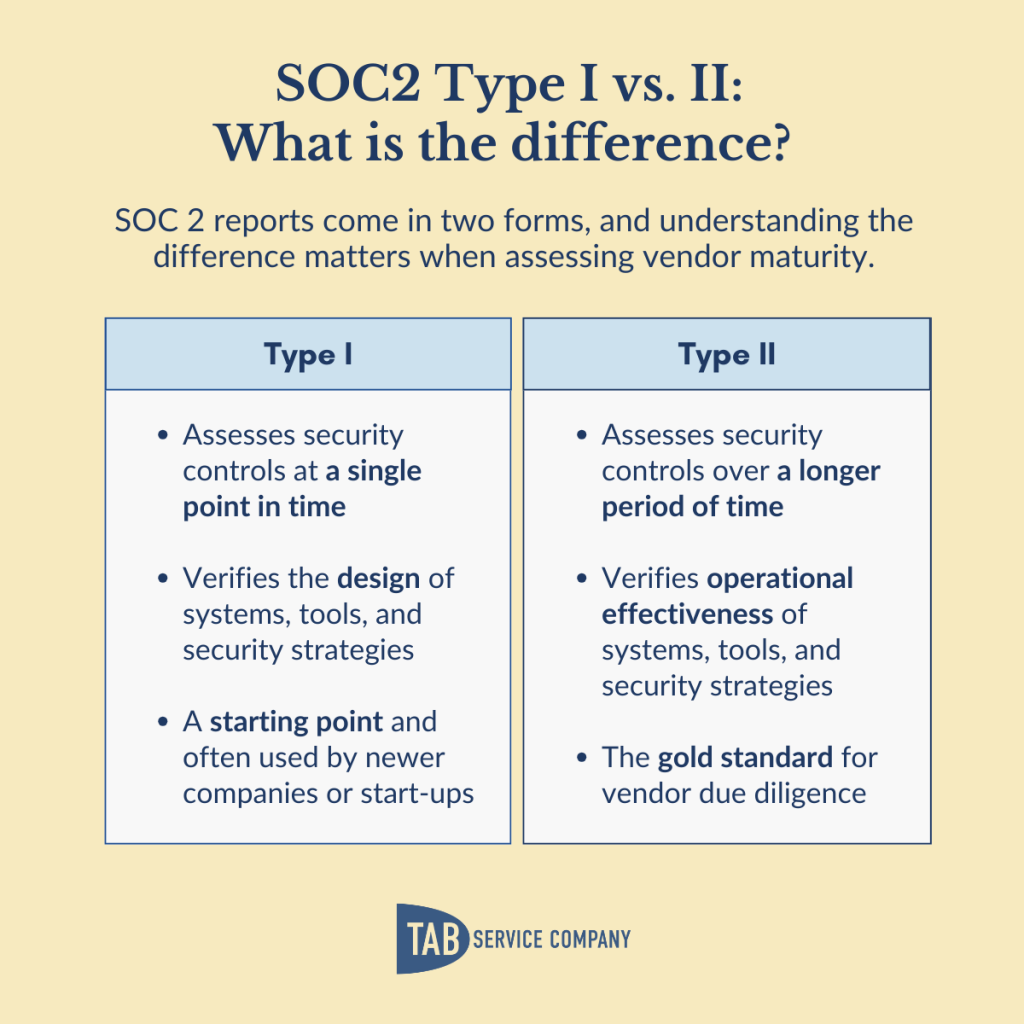
You’re evaluating vendors who will handle your sensitive data: customer records, financial information, tax documents, or employee files. Some vendors have SOC 2 Type I reports. Others have SOC 2 Type II. A few just say “SOC 2 compliant” without specifying which.
The difference matters significantly. A Type I report tells you a vendor’s security controls were designed properly at a point in time. A Type II report tells you those controls actually worked consistently, over a full year, and under real operating conditions. When you’re extending your security perimeter to a third party, that distinction is the difference between a promise and proof.
The Key Difference: Design vs. Proven Performance
SOC 2 Type I: Point-in-Time Assessment
A Type I report checks whether a company’s security controls are designed properly at a single point in time. The auditor reviews policies, procedures, and system descriptions to confirm the controls should work in theory:
- Controls are documented and policies exist
- The security framework is reasonable
- The company understands what controls should be in place
Type I is a meaningful credential — it represents real investment in building a security program — but it doesn’t verify that controls hold up in day-to-day operations.
SOC 2 Type II: Operational Effectiveness Over Time
A Type II report checks whether controls are not only designed properly but also working effectively over an extended period — minimum six months, typically a full year.
The auditor goes beyond reviewing documents. They test controls repeatedly throughout the audit period: Did access controls prevent unauthorized access? Were security incidents logged and handled properly? Were system privileges removed when employees left? The audit verifies that:
- Controls work effectively in real operations
- The company maintains controls consistently across 6–12 months
- The security framework holds up under actual business conditions — including high-volume periods, staff turnover, system changes, and deadline pressure
Why SOC 2 Type II Matters for Your Risk Profile
When you trust a vendor with your organization’s sensitive data, you’re extending your security perimeter. How well their controls work in practice directly affects your risk.
A vendor might show you a Type I report confirming their controls were well-designed several months ago. What you need to know is whether those controls held up every day since. Some examples of what gets tested during a Type II audit:
- Access controls: Reviewing terminated employee records and verifying system access was removed within required timeframes. Checking user access logs to confirm only authorized people accessed sensitive data.
- Security monitoring: Examining security event logs to confirm continuous monitoring happened. Verifying incidents were detected, logged, investigated, and resolved properly.
- Change management: Reviewing system changes to verify they followed documented procedures and were tested before going live.
- Data processing: Testing sample transactions to verify complete, accurate, and timely processing. Confirming data validation controls caught errors.
Questions to Ask Vendors About Their SOC 2 Compliance
When you’re actively evaluating a vendor, these are the questions that separate meaningful assurance from marketing language.
- “Do you have SOC 2 Type I or Type II attestation?” Ask for specific clarification. Some vendors say “SOC 2 compliant” without specifying which type — or without having a current report at all.
- “Can you share your most recent SOC 2 report under NDA?” Legitimate vendors will provide their report under a mutual Non-Disclosure Agreement. Reluctance to share is itself a signal.
- “When was the audit completed, and what period does it cover?” Recency matters. A Type II report completed 18 months ago is less reassuring than one completed last quarter. Annual audits should produce reports within the last 12 months.
- “If Type II, what was the audit period length?” Look for 12-month audit periods. Six months meets the minimum requirement but provides less assurance than a full year.
- “Were there any exceptions or findings in your most recent report?” Clean opinions with no exceptions demonstrate strong, sustained control effectiveness. Exceptions aren’t automatically disqualifying, but ask what remediation was taken.
- “Which Trust Service Criteria does your SOC 2 cover?” Not all audits cover the same criteria. For data processing vendors, look for Security, Processing Integrity, and Confidentiality at minimum.
- “Who conducts your SOC 2 audit?” Auditor quality matters. Nationally recognized CPA firms bring more rigorous standards than smaller or less specialized firms.
- “If Type I, what’s your timeline for Type II attestation?” Organizations typically run controls for 6–12 months after Type I before pursuing Type II. Understanding their roadmap shows whether they’re building toward comprehensive verification.
How to Read a SOC 2 Report
If a vendor shares their report, knowing what to look for makes it useful rather than overwhelming. SOC 2 reports are dense, but the key sections are straightforward.
The auditor’s opinion letter comes first and is the most important part. You’re looking for an unqualified opinion — language stating that controls were “suitably designed” (Type I) or “operating effectively” (Type II) throughout the period. A qualified opinion or adverse opinion indicates exceptions that weren’t resolved. An emphasis of matter paragraph flags something the auditor wants to draw attention to without modifying the opinion — worth reading carefully.
The description of the system explains what the vendor’s environment covers: which systems, which services, which data. Make sure the scope matches what you’re actually sending them.
The controls and test results table is the heart of the report for Type II. Each control is listed alongside the auditor’s test procedure and the result. Look for any rows marked as exceptions — these show where a control failed or wasn’t operating as described. A small number of exceptions with documented remediation is less concerning than repeated failures in the same area.
Subservice organizations are third parties the vendor relies on (cloud providers, data centers, etc.). The report will either include or exclude their controls — know which, because excluded subservice organizations represent a gap you may need to evaluate separately.
When SOC 2 Type I Makes Sense
Type I shouldn’t be dismissed. For newer vendors building their compliance programs, Type I represents genuine investment and commitment — documented policies, engaged auditors, a real security framework.
Type I works well for:
- Evaluating vendors for lower-risk, non-critical applications
- Preliminary vendor assessments before deeper review
- Assessing vendors actively working toward Type II with a defined timeline
If you’re evaluating a vendor with only Type I, ask about their Type II timeline and what controls they’ve been operating since the Type I was completed.
Make Type II Your Standard for Critical Systems
For the following situations, Type II should be your baseline requirement:
- Critical business systems your operations depend on
- Sensitive data including customer information, financial records, or regulated data
- High-volume processing where control failures would significantly impact your business
- Compliance-driven industries — healthcare, financial services, and higher education — with strict vendor requirements
- Long-term partnerships where sustained control effectiveness matters over time
Type II also streamlines enterprise procurement. Many vendor review processes specifically require it, and a clean 12-month report speeds due diligence significantly.
The Tab Service Company Standard: 20 Years of SOC 2 Type II
Tab Service Company has maintained SOC 2 Type II certification consecutively for over 20 years — predating the SOC 2 framework itself, through its predecessor audits, and through every annual cycle since.
That tenure means security controls aren’t a compliance exercise here. They’re operational infrastructure. They don’t slip during busy seasons, they don’t get skipped under deadline pressure, and they don’t depend on a single person to maintain.
Our SOC 2 Type II program includes:
- Annual audits by Plante Moran, one of the nation’s most respected CPA firms
- Annual penetration testing by HALOCK Security Labs
- Full 12-month audit periods with clean opinions and zero exceptions
- Coverage for Security, Processing Integrity, and Confidentiality
- HIPAA, FERPA, GLBA, GDPR, and CCPA compliance alongside SOC 2
Making the Right Choice for Your Organization
Type I provides valuable confirmation that controls are thoughtfully designed and the vendor has invested in building a security framework.
Type II provides comprehensive verification that controls work effectively and consistently in practice — across varying business conditions, over a sustained period, tested by an independent auditor.
For critical systems and sensitive data, Type II is the right standard. It provides the level of independent verification that supports a confident partnership decision.
Related Reading
- What to Look for in a BPO Partner
- How to Choose a Legal Document Scanning Provider
- What Is a Digital Mailroom?
- Security & Compliance at Tab Service Company
Partner with a Vendor That Takes Security Seriously
When you’re evaluating vendors for critical data processing, you need a partner with proven, sustained security practices — not just a recent audit.
Tab Service Company brings 20+ years of consecutive SOC 2 Type II compliance and deep expertise in secure data processing for healthcare, higher education, financial services and fintech, benefit fund administration, and legal.
Learn About Our Security & Compliance | Explore Our Services | Contact Our Team